Updated: How Zoom’s Recent Success Has Put Them Square in the Security Spotlight
Image via LinkedIn
P.T. Barnum is credited for saying,”There’s no such thing as bad publicity.” You may have heard other variations of this old saying, such as “There’s no such thing as bad press.” Does this apply to recent headlines about Zoom? If you have lost track, I will do my best to summarize and put it all in perspective.
Let’s start with “Zoom bombing,” the recent trend where malicious actors will join Zoom meetings and share pornography or other inappropriate and unwanted content. The trend started in 2019 with a vulnerability nicknamed “Prying Eye.” Cequence Security’s CQ Prime researchers (good hackers) found they could cycle through potential Zoom or Cisco Webex meeting IDs using API calls until they found a valid meeting ID. Once a valid meeting ID was discovered, a malicious actor could join the meeting as long as it did not require a password. Zoom responded by making meeting passwords required by default, but still an option. Cisco was already requiring meeting passwords. Neither company really acknowledged Prying-Eye as a security vulnerability at the time. Many meetings had simple passwords that were easily guessable.
Check Point security researchers then took it a step further and determined that they could accurately predict new Zoom meeting IDs approximately 4% of the time. Four percent may seem like a low success rate, but using bot networks, it became very easy for hackers to predict new Zoom meeting IDs, and Zoombombing became the script kiddies’ (young hackers) new favorite pastime. Pass the Zoom ID on the left-hand side.
Over the past couple months, the use of Zoom and other videoconferencing has skyrocketed, which means that more meeting IDs were being generated, and that, in turn, resulted in more Zoombombing.
Inexperienced users did not require passwords for their meetings. Others used personal meeting IDs and published them in their email signatures. Town councils, churches and schools started advertising their meetings on public websites and social media. “Join us for worship this Sunday at 10:30, here is the password…” This is basically the same as Tweeting, “I am leaving my key under the mat, here is my address…” Hackers had a field day and the dark web started sharing these meeting IDs and passwords.
Many experienced AV professionals would say that Zoombombing was essentially due to “user error.” But from a new user’s perspective, it’s a risk that should have been more clearly communicated to them.
As adoption of Zoom soared in March 2020, so did the criticism. Mainstream media outlets like Forbes put Zoom under the microscope, and began to point out some growing concerns over Zoom’s privacy policy. According to the privacy policy (as of early March 2020), Zoom reserved the right to collect and store users’ personal data, as well as share it with third-party vendors, including what it called “customer content” like videos, powerpoints, etc. Zoom responded to the Forbes article on March 27, 2020:
“Zoom takes its users’ privacy extremely seriously. Zoom only collects data from individuals using the Zoom platform as needed to provide the service and ensure it is delivered as effectively as possible. Zoom must collect basic technical information like users’ IP address, OS details and device details in order for the service to function properly.
“Zoom has layered safeguards in place to protect our users’ privacy, which includes preventing anyone, including Zoom employees, from directly accessing any data that users share during meetings, including – but not limited to – the video, audio and chat content of those meetings. Importantly, Zoom does not mine user data or sell user data of any kind to anyone.”
That was about a month ago and Zoom has since implemented a 90-day feature freeze in order to focus on the security concerns. As part of this plan, Zoom has formed a CISO Council and Advisory Board to address the vulnerabilities, combining the experience from NTT Data, HSBC, Ellie Mae, Procore, Uber, VMware, Netflix and EA experts, along with Alex Stamos, former chief security officer at Facebook.
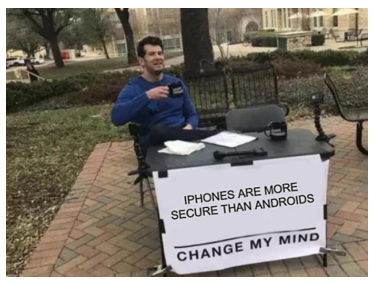 The “bad press” continued into April, as reports of hackers targeting Android users by distributing malicious clones of the Zoom app. In Zoom’s defense, this is actually not a Zoom issue, but part of a larger issue of malicious Android apps being distributed outside of the Google Play Store. Android apps can be downloaded from any website and there is no guarantee that what you are downloading is not malware. Conversely, iPhone/iPad users can only download iOS apps through the Apple Store, which scans all apps for vulnerabilities before they are available. Android apps are in the wild west when it comes to security.
The “bad press” continued into April, as reports of hackers targeting Android users by distributing malicious clones of the Zoom app. In Zoom’s defense, this is actually not a Zoom issue, but part of a larger issue of malicious Android apps being distributed outside of the Google Play Store. Android apps can be downloaded from any website and there is no guarantee that what you are downloading is not malware. Conversely, iPhone/iPad users can only download iOS apps through the Apple Store, which scans all apps for vulnerabilities before they are available. Android apps are in the wild west when it comes to security.
Two days later, on April 3, reports emerged that Zoom’s so-called “end-to-end encryption” was not exactly what many people thought. Zoom admitted its definition of “end-to end encryption” was different from the definition held by the security community because the data was only encrypted between the users and the Zoom server. AV professionals could understand this: Zoom needed to decrypt the video and audio in order to perform echo cancelation and combine the streams. Some say that Zoom should have been more transparent about it, and should make it clearer to the users that the Zoom meeting host can record the calls. Due to the lack of transparency, many claimed that Zoom was violating GDPR. GDPR insists that consent for collecting personal data must be freely given. Moreover, if there is an imbalance of power between the two parties, it cannot be a free choice and thus, any consent obtained is invalid.
Around the same time, reports emerged that the keys used to encrypt and decrypt Zoom meetings were being sent to China, even if the participants were located in other countries. Zoom’s CEO Eric Yuan further admitted on CBNC’s Mad Money that a small percentage of Zoom calls are routed through China, even if no one on the call is located in China. Whoa! The company released a new version of Zoom this past weekend, which allows PAYING users to opt-in to servers located in certain geographic regions and/or opt-out of other regions. But for non-paying Zoom users, any Zoom call still can be routed through China.
About a week later, a class-action suit was filed, claiming that investors and users were misled by Zoom into thinking that the platform was more secure. The next day researchers announced they had found a database of Zoom credentials on the dark web that was “too small to suggest an unknown data breach of Zoom itself, but too large to suggest a random collection of details found online.”
Governments across the globe, from Germany to the U.S. Senate have warned their staff not the use Zoom due to the security concerns. The New York City Department of Education has prohibited the use of Zoom in schools and other school districts are likely to do the same. There is a more secure version of Zoom that is specifically designed to be used by governments, but most users only utilize the standard version.
Zoom released a new security update this past weekend and continues its 90-day plan to improve security. Working with experts like Alex Stamos and others on its CISO Council and Advisory Board, Zoom continues to address security. Zoom’s CEO, Eric Yuan, has managed to navigate the bad press with his charming personality and transparent attitude. Mr. Yuan will be featured during rAVe’s own LAVNCH Week this week.
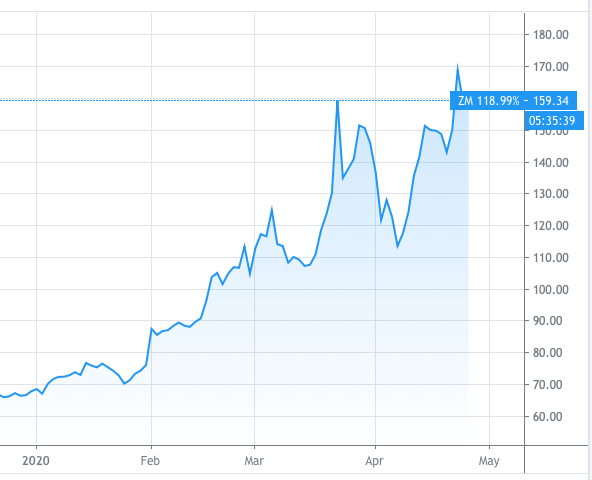
Zoom’s stock price on April 27, 2020
So, does the old saying, “There’s no such thing as bad press,” hold true for Zoom? I think it does. Zoom (ZM) closed at $159.38 per share on Friday April 24, 2020, about 4% down from its all-time high of $164.94 per share put in on March 23, only five weeks ago. Zoom will continue to receive criticism and there will certainly be some selling pressure, as some disgruntled shareholders who bought in near the high mark will bail out the first day their trades turn green. But once Zoom breaks the $165 price level, I would expect it to continue higher, just like it continues to take market share from other video conference providers.
Update: Zoom released a new blog on April 27, 2020 that addresses some of the issues from this column. You can read it here.
DISCLOSURE: The author, Paul Konikowski, owns a small amount of Zoom (ZM) shares, along with American Tower Corporation (AMT), Starbucks (SBUX), Wendy’s (WEN), Disney (DIS) and SPDR S&P 500 ETF TRUST (SPY).